HashiCorp Boundary Enterprise With Crack
HashiCorp Boundary Enterprise 0.16.2 Crack, a cutting-edge solution that redefines secure access for modern infrastructure. Designed by HashiCorp, a leader in cloud infrastructure automation, Boundary Enterprise offers a dynamic approach to access management, allowing organizations to securely connect and access resources across diverse environments. With a focus on simplicity and scalability, this latest version introduces powerful features to enhance identity-based access controls and streamline the management of secure access policies. From on-premises servers to cloud-based infrastructure, HashiCorp Boundary Enterprise Full Crack sets a new standard for secure access, providing organizations with the tools they need to achieve efficient and secure access to critical resources.
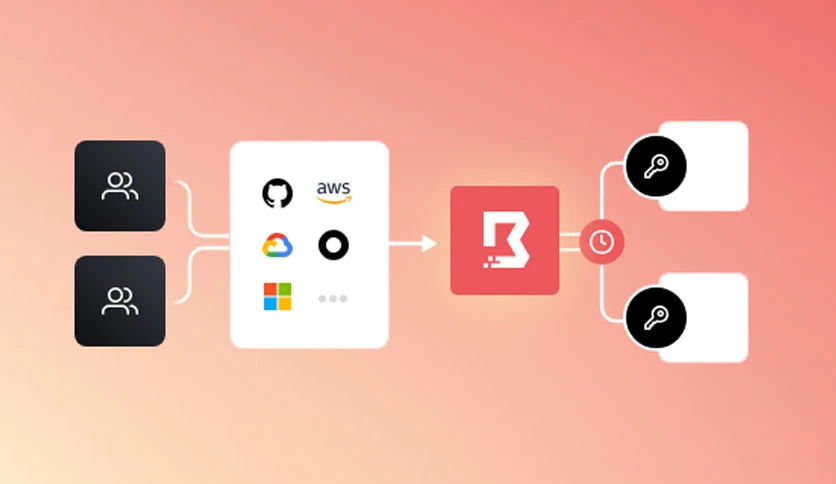
HashiCorp Boundary Enterprise Torrent Crack brings a wealth of features to address the evolving challenges of secure access. The software offers dynamic host catalogs, simplifying access management by dynamically updating host information. With session recording and playback capabilities, organizations can achieve greater visibility into user activities and maintain a comprehensive audit trail for security compliance. Boundary Enterprise Mac Crack integrates seamlessly with popular identity providers, allowing organizations to leverage existing authentication systems. This version also introduces enhanced support for multi-datacenter architectures, enabling organizations to scale their secure access solutions across distributed environments. Explore the future of secure access with HashiCorp Boundary Enterprise Latest Crack, where innovation meets security in the realm of infrastructure access management.
HashiCorp Boundary Enterprise Crack Features
Dynamic Host Catalogs
Simplify access management with dynamic host catalogs that automatically update host information, ensuring efficient and accurate access control across diverse environments.
Session Recording and Playback
Enhance visibility and security compliance with session recording and playback capabilities, allowing organizations to maintain comprehensive audit trails of user activities.
Integration with Identity Providers
Seamlessly integrate Boundary Enterprise with popular identity providers, enabling organizations to leverage existing authentication systems for streamlined and secure access management.
Multi-Datacenter Support
Scale secure access solutions across distributed environments with enhanced support for multi-datacenter architectures, ensuring flexibility and scalability in infrastructure access management.
System Requirements
Operating System:
Linux or Windows
Processor:
64-bit architecture
RAM:
4 GB or more
Storage:
20 GB of free space for installation
HashiCorp Boundary Enterprise 0.16.2 100% Working Keys 2024
HashiCorp Boundary Enterprise Serial Key
VNXXO-VGYO8-2A6HN-SULOC-36685
KPUD9-Y9MW7-B7Z6N-OWVFH-JX35S
HashiCorp Boundary Enterprise Activation Code
GBOLB-JUB7G-9OF6T-8112P-DJEOZ
OL3AE-F31M1-FCPNU-EU49P-NEC48
HashiCorp Boundary Enterprise License Key
PIQLM-O5TUG-G0E5A-8MQ0X-5VM1L
HI6G2-TPLZZ-2LN2T-4P9DT-REPOM
HashiCorp Boundary Enterprise Product Key
10AFJ-9WJI8-FHB21-6UR6T-UDJKO
DW4T0-R59R9-L6R8H-B6LRM-5720O
How To Crack & Install HashiCorp Boundary Enterprise 0.16.2
- First download the latest version.
- Uninstall the previous version with Revo Uninstaller Pro, If Installed.
- Note Turn off the Virus Guard.
- After downloading Unpack or extract the rar file and open setup (use Winrar to extract).
- Install the setup after installation close it from everywhere.
- Please use Keygen to activate the program.
- After all of these enjoy the HashiCorp Boundary Enterprise 0.16.2 Crack Latest Version 2024.
